| Developer: | BlackBerry Limited (20) | ||
| Price: | Free | ||
| Rankings: | 0 | ||
| Reviews: | 0 Write a Review | ||
| Lists: | 0 + 0 | ||
| Points: | 0 + 0 ¡ | ||
| Mac App Store | |||
Description
Securing connections between users and business systems that lie beyond your firewall is essential and presents several challenges, particularly when users are working remotely, and their devices connect to networks beyond your organization’s control.
Until recently, many organizations have relied on a traditional “castle-and-moat” approach to network security where defenses surround the perimeter of the network, but once someone has crossed the threshold or tunneled in, they are completely trusted. Network security experts now understand that this method is not sufficient for several reasons:
• Use of cloud-based services and SaaS applications is increasing, resulting in an extended and dynamic network perimeter where much of your proprietary data is stored outside of your physical location and more of your critical IT services reside in the cloud.
• Sophisticated phishing and social-engineering attacks can exploit users already inside the network.
• Using public Wi-Fi access points exposes various types of man-in-the-middle attacks, even for TLS traffic.
• Business partners, contractors, and large numbers of remote employees need access to your organization's tools and data to do their jobs, even when they are connected to networks outside of your perimeter.
• Performance deteriorates when you send traffic destined for cloud and SaaS services through your organization’s firewall and network.
Security-conscious organizations are moving to a Zero Trust approach to modernize network security while simultaneously enhancing and improving the network experience for end users. Every user, endpoint, and network are assumed to be potentially hostile. In Zero Trust security, no user can access anything until they prove who they are, that their access is authorized, that they’re not acting maliciously, and that the Wi-Fi or cellular network they are connected to is not compromised.
The question for organizations is how to implement a Zero Trust network access model that is continuously secure but still allows users to access all of the resources they need without losing productivity though frequent authentication prompts and reduced connection speeds. BlackBerry’s answer to this question is CylanceGATEWAY.
CylanceGATEWAY enables AI assisted Zero Trust Network Access to enterprise SaaS & On-prem apps and is focused on earning trust across endpoint & network, continuously validates that trust at every event or transaction to deliver a Zero Touch experience that improves security with limited user interruption.
BlackBerry offers suites of products that, together, provide a total solution for Zero Trust with full coverage across the full spectrum of devices, network, apps and people. CylanceGATEWAY has these advantages:
• Zero Trust Network Access to On-prem & SaaS apps
• Provides a path from Zero Trust architecture to Zero Touch experience powered by strong AI
• Works across all endpoint types for complete coverage and better insight into trusted behavior
• Provides continuous monitoring and threat detection to facilitate data and AI integrity
• Provides contextual and continuous authentication that spans endpoints, networks, apps, and people
• Simplifies administration, reduces costs, and eliminates unnecessary friction
CylanceGATEWAY is the latest addition to BlackBerry® product suites, designed to provide network security as a service from all of your endpoints and to all of your cloud access points and on-prem resources with continuous authentication and authorization leveraging multiple contexts.
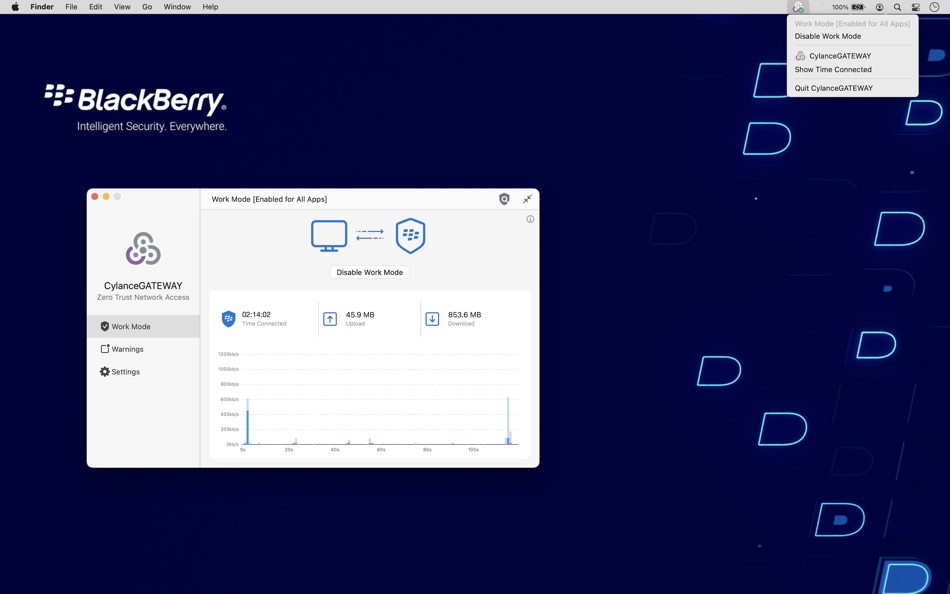
Screenshots
Price History
- Today: Free
- Minimum: Free
- Maximum: Free
Track prices
Developer
- BlackBerry Limited
- Platforms: Android Apps (13) iOS Apps (5) macOS Apps (1) Windows Apps (1)
- Lists: 0 + 0
- Points: 5 + 166,681 ¡
- Rankings: 0
- Reviews: 0
- Discounts: 0
- Videos: 0
- RSS: Subscribe
Points
0 ☹️
Rankings
0 ☹️
Lists
0 ☹️
Reviews
Be the first to review 🌟
Additional Information
Contacts
«CylanceGATEWAY» is a Utilities app for macOS, developed by «BlackBerry Limited». It was first released on and last updated on . This app is currently free. This app has not yet received any ratings or reviews on AppAgg. Available languages: English, French, German, Japanese. AppAgg continuously tracks the price history, ratings, and user feedback for «CylanceGATEWAY». Subscribe to this app or follow its RSS feed to get notified about future discounts or updates.
- 🌟 Share
- Mac App Store
You may also like
-
- DuckDuckGo, Duck.ai (optional)
- macOS Apps: Utilities By: DuckDuckGo, Inc.
- * Free
- Lists: 11 + 3 Rankings: 0 Reviews: 0
- Points: 12 + 2,240,518 (4.9) Version: 7.196.0 At DuckDuckGo, we believe the best way to protect your personal information from hackers, scammers, and privacy-invasive companies is to stop it from being collected at all. That's why ⥯
-
- NordVPN: VPN Fast & Secure
- macOS Apps: Utilities By: Nordvpn S.A.
- * Free
- Lists: 0 + 4 Rankings: 0 Reviews: 0
- Points: 4 + 642,539 (4.7) Version: 8.58.0 Looking for a way to have more privacy online? Here it is! With NordVPN, one tap is all you need to change your IP address, protect your browsing from snoopers, and enjoy the internet ... ⥯
-
- Color Widgets
- macOS Apps: Utilities By: MM Apps, Inc.
- Free
- Lists: 0 + 2 Rankings: 0 Reviews: 0
- Points: 6 + 494,651 (4.6) Version: 8.0.4 Color Widgets makes adding aesthetic and handy widgets to your Home Screen and Lock Screen easy. Browse thousands of predesigned widgets or, better yet, design your own with the ... ⥯
-
- Free VPN by Free VPN .org™
- macOS Apps: Utilities By: Free VPN LLC
- Free
- Lists: 0 + 1 Rankings: 0 Reviews: 0
- Points: 2 + 435,570 (4.5) Version: 4.040 Free VPN, #1 - VPN for secure browsing on iPhone, iPad & Mac. Tired of slow connections, privacy risks or can't access your favorite shows and videos. Free VPN by Free VPN.org™ gives ... ⥯
-
- ExpressVPN · Secure & Fast VPN
- macOS Apps: Utilities By: Express VPN
- Free
- Lists: 0 + 1 Rankings: 0 Reviews: 0
- Points: 2 + 405,861 (4.7) Version: 12.34.0 ExpressVPN: Premium VPN for Security, Privacy, and Blazing Fast Streaming Surf the web safely with just a few taps. ExpressVPN is a premium VPN service designed for ultra-fast ... ⥯
-
- VPNIFY - Unlimited VPN
- macOS Apps: Utilities By: Neonetworks solution ltd
- Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 2 + 98,419 (4.5) Version: 2.3.42 vpnify is the best VPN & UNLIMITED 100% FREE high speed VPN Proxy on for your iOS device. It is highly secure with military-grade encryption so you can safely navigate public, business ⥯
-
- V2Box - V2ray Client
- macOS Apps: Utilities By: techlaim
- Free
- Lists: 3 + 0 Rankings: 0 Reviews: 0
- Points: 16 + 83,219 (4.7) Version: 9.8.7 V2box - VPN Internet network proxy , Supports multiple proxy protocols, such as Shadowsocks, V2ray, Vmess, Trojan , SSH , Socks Features: - Support for adding custom servers proxy ... ⥯
-
- VPN - Free VPN Potato ™
- macOS Apps: Utilities By: FREE VPN POTATO PTE. LTD.
- Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 2 + 65,522 (4.6) Version: 22.9 PotatoVPN protects your online privacy as an unlimited VPN proxy, offering a super service for those seeking a free VPN for your iPhone. Enjoy ultra-fast speeds, unlimited bandwidth, ... ⥯
-
- AdBlock Pro for Safari
- macOS Apps: Utilities By: Crypto Inc.
- Free
- Lists: 4 + 3 Rankings: 0 Reviews: 0
- Points: 31 + 65,100 (4.5) Version: 12.0.1 Since 2015, AdBlock Pro for Safari has been trusted by millions of users and featured by Apple multiple times. Enhance your browsing experience on iPhone, iPad, Mac, and Vision Pro ... ⥯
-
- Flip Clock - digital widgets
- macOS Apps: Utilities By: 翠玲 施
- Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 4 + 62,641 (4.6) Version: 6.14 Flip Clock is a classic desktop digital clock. The desktop clock widget supports displaying seconds and a calendar. Clock can be displayed on lock screen and standby screen. - Show ... ⥯
-
- Deliveries: a package tracker
- macOS Apps: Utilities By: Junecloud LLC
- Free
- Lists: 3 + 9 Rankings: 0 Reviews: 0
- Points: 9 + 34,298 (4.7) Version: 9.6.1 Deliveries helps you keep track of all your packages, so you always know when they re going to arrive. Whether it's the latest gadget you've preordered online, or a new graphic novel ... ⥯
-
- VPN Lumos: Open & Connect USA
- macOS Apps: Utilities By: LUMOS, OOO
- Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 4 + 32,217 (4.5) Version: 2.23 VPN Lumos offers you a fast, private and secure internet connection. Change your IP address, access social networks, streaming, watch TV, browse movie websites, play games and more ... ⥯
-
- Planet Free VPN ™ Super Proxy
- macOS Apps: Utilities By: FREE VPN PLANET S R L
- Free
- Lists: 1 + 0 Rankings: 0 Reviews: 0
- Points: 1 + 31,183 (4.6) Version: 4.9.15(6) Planet VPN - 100% Free, unlimited and secure VPN. There are no alternatives to our app in all of AppStore. The safety and anonymity of our users is a priority for us! Unlike other VPN ... ⥯
-
- Authenticator App - OneAuth
- macOS Apps: Utilities By: Zoho Corporation
- Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 1 + 29,906 (4.7) Version: 4.1.5 OneAuth is an industry standard authenticator app developed by Zoho. You can now enable TFA and secure all your online accounts like Twitter, Facebook, LinkedIn, and more. Over 1 ... ⥯